SaaS Security: What You Need To Know
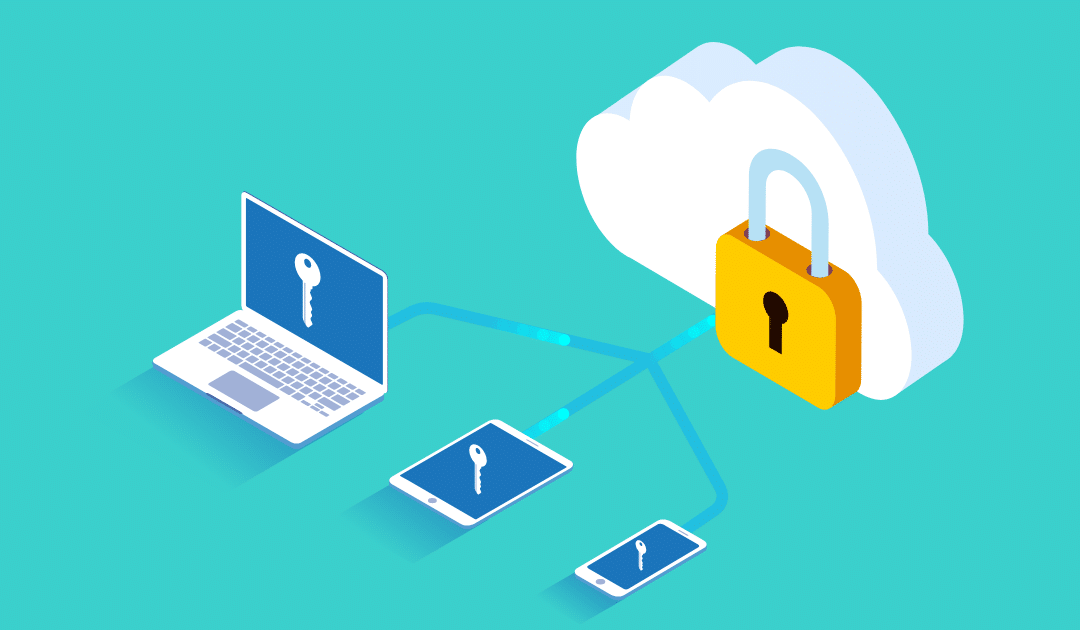
Security is a critical part of any SaaS application. SaaS security risks are the responsibility of SaaS providers and SaaS users, but not without some collaboration to make sure that everyone takes their role seriously. SaaS security controls rely on a few important factors such as data encryption, authentication & authorization, access control, application security, and patching. In this article, we’ll discuss what you need to know about SaaS security as well as how it’s achieved with SaaS security controls and principles.
Who Is Responsible For SaaS security?
SaaS providers are responsible for SaaS security. SaaS users rely on SaaS providers to ensure that they’re using secure SaaS applications. Saas development services play a crucial role in implementing robust security measures, ensuring that the software is designed with the best practices for data encryption, authentication, access control, and other critical security principles.
When a SaaS provider becomes aware of a vulnerability, it is its responsibility to issue a prompt patch or an update to maintain the integrity and safety of its customers’ information as well as its infrastructure.
Understanding the shared responsibility for a SaaS environment’s security is critical to its process. It’s essential for SaaS users to be aware of vulnerabilities and their risks. This awareness is where concepts like cyber asset attack surface management come into play. This helps teams understand what SaaS providers are doing to protect your information, and integrate strategies like data description, multi-factor authentication, etc., enabling you to make more informed decisions.
There’s a good reason why people say “the cloud” when they really mean SaaS: it feels safer because data isn’t sitting directly on your physical server or local hard drive anymore. Especially if they’re using private cloud, things get even more secure. Even if all precautions have been taken by both SaaS providers and SaaS users, SaaS security vulnerabilities are still an overarching risk.
In some sense, no software application is ever 100% safe from cyber threats because hackers always find ways around existing technology – this includes cloud-based apps like those hosted by SaaS providers. In general, however, most SaaS data breaches can be attributed to weak authentication controls (i.e., poor username/password management), SaaS security vulnerabilities, and SaaS data breaches.
What Are SaaS Security Controls And Principles?
SaaS security principles are the safeguards put in place to protect data and systems from unauthorized access, use, disclosure, modification, or ruin. SaaS providers must adhere to certain SaaS security principles and follow SaaS security tips to ensure that their customers’ data is protected at all times.
Some of these key SaaS security principles include:
- Data encryption: This ensures that data is unreadable without proper authorization and prevents hackers from stealing or altering it
- Authentication & Authorization: These mechanisms verify the identity of users and control what they can see and do within a system
- Access Control: Refers to restriction of access to authorized users. Thus preventing access to sensitive information by unauthorized individuals.
- Application Security: Protecting against vulnerabilities in web applications is critical to SaaS security. Web application security testing assists you in identifying exploitable flaws in your web applications.
- Patching: Prevent hackers from targeting known vulnerabilities by ensuring that these are patched as soon as possible.
SaaS security is achieved at the provider level using models designed by companies like GuidePoint Security to protect customer data by separating it into discrete chunks that can be managed, monitored, and secured independently. This also allows customers to use the same application without compromising their security or performance. To provide this level of isolation, SaaS providers deploy a multitenant architecture that enables them to share resources among multiple customers while ensuring that each customer’s data is completely secure and private.
This multitenant architecture includes a combination of people, processes, and technology controls.
- People Controls: SaaS providers rely on their staff to implement and maintain SaaS security controls. This includes implementing data encryption, authentication & authorization mechanisms, access control measures, application security controls, and patching processes. Staff must be mandatorily trained on the usage of these safeguards and what their role is in protecting customer data.
- Process Controls: SaaS providers also have process controls in place that help ensure the safety of their customers’ data. These include change management procedures (minimizing the risk of unauthorized changes to systems), incident response plans (rapid response to contain any breaches), and disaster recovery plans (ensuring 24*7 availability of customer data). SaaS providers must clearly define account management procedures that specify the roles and responsibilities of different employees. Along with this service-level agreements (SLAs) must specify SaaS performance standards.
- Technology Controls: SaaS providers rely on a wide range of technology controls to protect their customers’ data. These include firewalls, intrusion detection/prevention systems (IDS/IPS), malware protection, and data loss prevention.
SaaS Security Checklist
In order to help SaaS providers protect their customers’ data, the Cloud Security Alliance (CSA) has developed a SaaS security checklist. This checklist includes a variety of controls that SaaS providers can use to safeguard customer data.
The CSA SaaS security checklist covers the following areas:
- Access Control
- Authentication
- Data Classification & Handling
- Data Encryption
- Endpoint Security
- Information Security Management
- Network Security
- Patch Management
- Physical Security Controls
- Security Policies
- System & Application Security
- Third-Party Management
- Training & Awareness
- Vulnerability Scanning & Assessment
SaaS security is a critical issue for businesses of all sizes. By understanding the risks and implementing the appropriate controls, SaaS providers can help ensure that their customers’ data is safe and secure.
Benefits of SaaS Security
- SaaS providers ensure SaaS security by implementing a multitenant architecture. SaaS’s security model separates customer data into various parts that can be managed, monitored, and secured independently.
- It also helps SaaS providers comply with regulations such as the Health Insurance Portability and Accountability Act (HIPAA), which requires SaaS providers to implement certain safeguards for protecting sensitive health information.
- Security breaches can cause significant losses, but they are often avoidable by using proper SaaS security measures. SaaS providers can implement SaaS security controls to improve SaaS performance and increase the reliability of their service, which in turn helps them secure more customers.
- The growth rate for SaaS subscriptions has been increasing significantly over the past few years and was projected to reach $46.34 billion by this year. The SaaS security model has been a key factor in the growth of SaaS, helping ensure that customer data is safe and secure.
The Risks Associated With SaaS Security
These are the most common SaaS risks:
- SaaS Vulnerabilities (i.e. weak authentication controls) – This is when a hacker finds an exploit in one of the underlying libraries or operating systems used to build your SaaS app and uses this weakness as leverage against you and your data.
- SaaS Data Breaches – This is when hackers gain access to your SaaS account and download or steal your data. Once outside the walls of your organization, this stolen information can be used for all sorts of nefarious purposes such as identity theft, blackmail, and corporate espionage.
- Insider Threats – These are people who already have authorized access to sensitive company data but misuse that access for personal gain or malicious intent. A recent study by the Ponemon Institute showed that insider threat programs are now one of the most common causes of data breaches.
How SaaS Security Risks Are Managed?
The best way for SaaS providers and SaaS users to manage SaaS security risks is through collaboration. By working together, the two parties can identify which factors pose a risk so they can be eliminated or mitigated accordingly. Collaboration also makes it easier for both sides of the equation to implement policies and procedures around authentication controls, access control lists (ACLs), data encryption practices, patch management processes, etc. This increases overall awareness about how data flows throughout SaaS applications while minimizing potential threats on multiple levels – not just security, but also performance and functionality.
Conclusion
This article has discussed SaaS security in detail while mentioning the responsible parties, its security principles, and controls that make it a winning security model along with the risks associated and the benefits that outweigh them. To summarize, SaaS security is essential for safeguarding your company’s data. By following certain regulations and utilizing its multitenant architecture, you can provide your organization with a valuable degree of security.